You Clicked a Legitimate-Looking Link. You Entered Your Password.
You Were Already Compromised.
That’s the quiet danger of proxy phishing.
Unlike traditional phishing, which fakes a website, proxy phishing sits invisibly between you and the real one. You never notice anything wrong.
That’s exactly what makes it so effective.
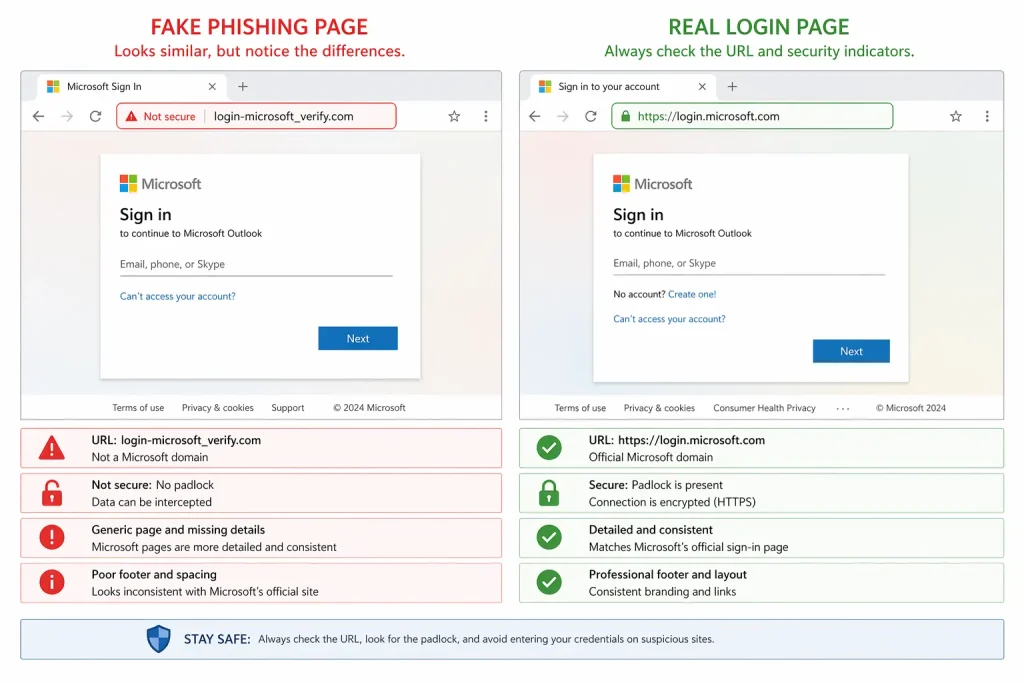
What Is Regular Phishing?
Traditional phishing is the older, simpler attack.
A cybercriminal creates a fake version of a trusted website, your bank, your email provider, your company portal and tricks you into entering your credentials there.
The signs are usually detectable if you know what to look for:
- Suspicious URLs (e.g. paypa1.com instead of paypal.com)
- Poor design or broken layouts
- Generic greetings like “Dear User”
It’s a blunt instrument. Security tools and awareness training have made it easier to catch.
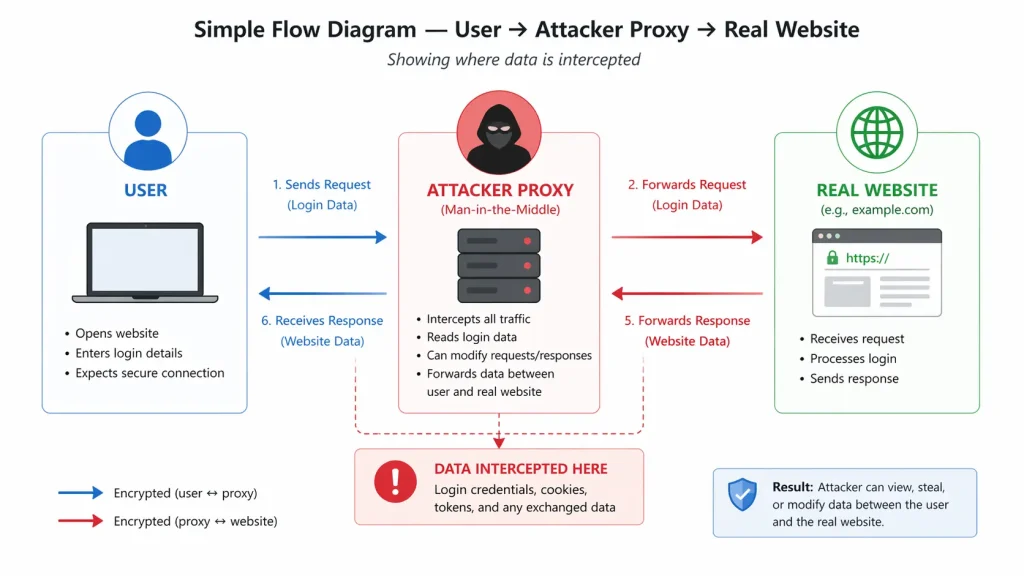
What Is Proxy Phishing And Why Is It Worse?
Proxy phishing is a more sophisticated evolution. Instead of showing you a fake site, the attacker places a reverse proxy server between you and the legitimate website.
Here’s how it works:
- You receive a link, it looks real, and often it’s the real domain.
- You click it and land on what appears to be the genuine site.
- Every action you take passes through the attacker’s proxy server.
- Your credentials, session tokens, and even MFA codes are captured in real time.
“Proxy phishing doesn’t fake the destination. It hijacks the journey.”
This is what makes it dangerous. Even two-factor authentication (2FA) can be bypassed because the attacker captures your session token the moment you log in successfully.
Proxy Phishing vs. Regular Phishing: Key Differences
| Factor | Regular Phishing | Proxy Phishing |
| Method | Fake website | Real site via malicious proxy |
| Detection | Easier, fake URLs, poor design | Very hard, everything looks real |
| Bypasses 2FA? | No | Yes, in many cases |
| Target | Broad, mass attacks | Targeted, high-value individuals |
| Sophistication | Low to medium | High |
Real-World Example
Tools like Evilginx and Modlishka are openly available reverse proxy frameworks that attackers use to run proxy phishing campaigns. They require minimal setup and can defeat standard login protections within minutes.
Security researchers have documented campaigns targeting Microsoft 365, Google Workspace, and banking platforms using exactly this method.
How to Protect Yourself and Your Business
- Use FIDO2 / Hardware Security Keys: Physical security keys (like YubiKey) are the most reliable defence. They bind authentication to the legitimate domain, a proxy cannot replicate this handshake.
- Enable Phishing-Resistant MFA: Standard SMS or app-based 2FA can be bypassed. Upgrade to FIDO2-based authentication wherever possible.
- Check URLs Carefully Every Time: Even when a page looks real, verify the URL. Look for HTTPS and confirm the exact domain, not a subdomain or lookalike.
- Use a Password Manager: Password managers auto-fill credentials only on the exact registered domain. If the URL doesn’t match, it won’t fill, giving you an automatic warning.
- Deploy Anti-Phishing Tools at the Organizational Level: Tools like Microsoft Defender, Cloudflare Gateway, and Proofpoint can detect and block known proxy phishing infrastructure before it reaches your employees.
- Train Your Team Regularly: Awareness is still your first line of defence. Run simulated phishing tests, educate employees on session hijacking, and make reporting suspicious links frictionless.
“The best cybersecurity tool you have is a team that knows what to look for.”
Challenges
No solution is foolproof.
Proxy phishing is evolving rapidly; attackers continuously adapt to detection methods. Even FIDO2, while highly effective, requires organisational adoption, which takes time and budget.
The honest reality: layered defence is the only reliable approach. No single tool stops everything.
Key Takeaways
- Regular phishing fakes a site, proxy phishing hijacks your real session.
- Proxy phishing can bypass standard 2FA, making it significantly more dangerous.
- FIDO2 hardware keys are currently the strongest defense available.
- Password managers act as an automatic proxy phishing detector.
- Employee awareness remains a critical, non-negotiable layer of protection.
Final Thought
Cybercriminals aren’t getting less creative; they’re getting more patient and precise.
Proxy phishing is proof that the threat has matured well beyond obvious fake emails and broken layouts.
The question worth asking isn’t “Would I fall for a phishing attack?“
It’s “Would I notice if someone was already sitting between me and every site I log into?“
That shift in thinking is where real security begins.